[CVE-2021–34785] Cisco BroadWorks - Privileged Escalation
Hello Everyone! Today I will talk about my last findings at Cisco products BroadSoft BroadWorks, one of the Cisco's products.
CVE-2021–34785: IDOR lead to privileges escalation “Admin account takeover”
Content
BroadWorks structure
At BroadWorks, we have an Admins group which have admins with write and read privileges and other admins with read-only privileges.
Read and Write: he can modify his data and other admins' data. Also, he can add users, change system preferences, delete users, and fully control the system
Read-only: he can modify his data and delete his account. He doesn’t have any other privileges “In my case”
I’ve got the second role (Read-only) and my task is trying to escalate my privileges to have Read and Write actions.
Exploitation
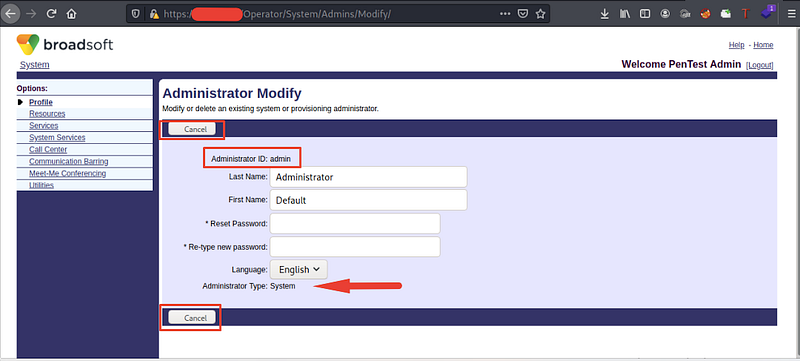
If you tried to view system users, we have 2 users: Admin and PentestAdmin. My user is PentestAdmin which has low privileges, reads his data only. User Admin has full control of the system

I tried to enumerate the admin account to know what allowed functions, but unfortunately! There’s no allowed function to use at the Admin profile, I can view the data only, but at ll, I know the firstname, lastname and adminID
After that, I tried to enumerate my account and found that I have 2 allowed functions delete the account and change the password without asking you for your old password, weird right?!

I entered a new password and intercepted the request to know what’s the request parameters. I’ve found that we have firstname, lastname and loginid required parameters because I tried to delete loginid but unfortunately! The request failed
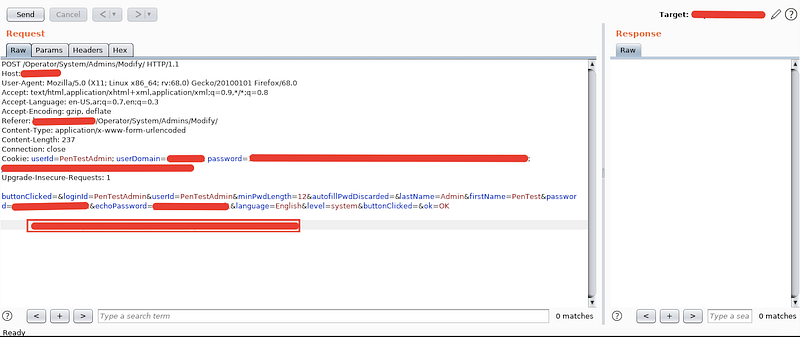
At all, it’s not a problem because I have privileges to read all users' data, so I know this data from the admin profile.
The final step is replacing your data with Admin data and sending the request. It returns 200 OK and to check, I tried to log in with the new password, and Bingo! You take over the admin account by changing his password ❤
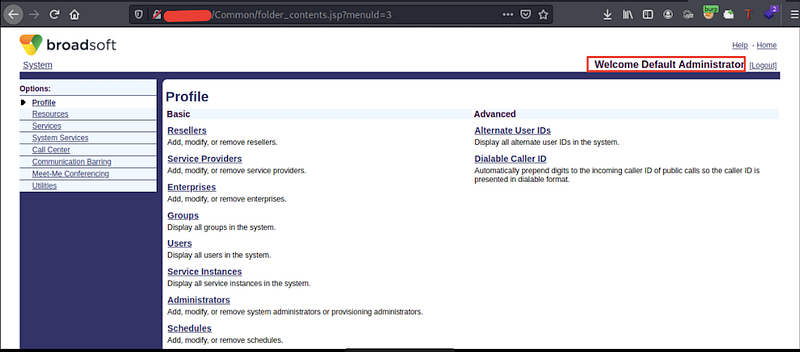

To make POC, I’ve created a new user SecmeterPOC with writing and reading privileges.

After reviewing the Admin board

Weakness points
At the change password function, it MUST ask me for the old password and if I forget it, it should ask me to contact the system administrator.
There’s no CSRF token attached with the user session to protect the system from performing the same attack using CSRF [I have tried it and successed]
To delete an account, it MUST ask the user to enter his password or any security question
Thanks for reading <3 Stay in touch
Last updated