Blue Walkthrough
Hello Everyone! Here we come back again with one of HackTheBox easy machines “Blue”, let’s take a look at its info and then get started…
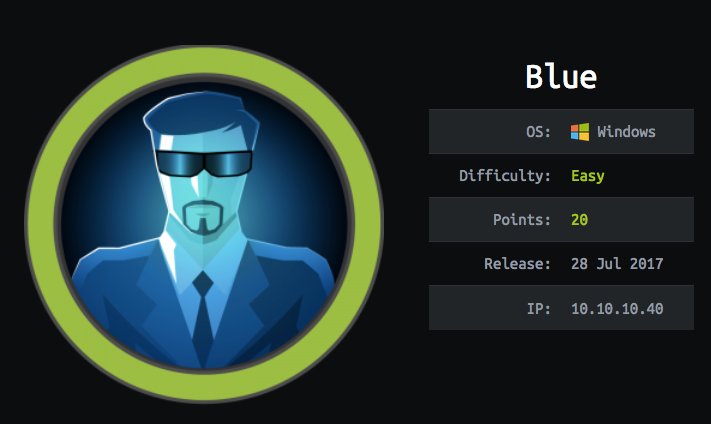
As you can see it’s easy and based on Windows OS. Let’s get started…
DNS Enumeration
We will start our way with nmap scan to get all open ports, services, OS info and more info as you will see later in this blog post.
the results:
As you can see we have more and more open ports but the interesting port which we need to focus on is smb and you should note 2 dangerous things in these results
from these results you should know that the smb server enable anyone to login and list the directories, so we will do 2 tasks:
Try to brute force the
smbcredentials and getusernameandpasswordby usingbrutespraytool (available on GitHub)Try to login to
smband list all files by usingsmbclientwith the credentials from step 1
Use brutespray
to use this tool we will need the gnmap file which we generate it from nmap scan and run this command → brutespray -f blue.gnmap

As you can see we now have 2 usernames and 2 passwords related to the service which worked on smb server, let’s go to the next step…
Use smbclient
this tool manage you to login to the server with your username and password as follows → smbclient -L \\10.10.10.40 and it will ask you for the password, remember that from nmap scan results the password is not required, but we will insert it to take admin privileges, I hope that :)

Now we have the directories, but we don’t have an access to open them, let’s search for another exploitation method…
Exploitation
One of the advantages of nmap is nmap scripts, my opinion it’s wonderful, so we will use it to scan this port 445 and get us back the exploitation form it’s CVE scripts scan as follows

Now we know that it’s vulnerable by ms17–010, let’s search about it on metasploit

As you can see we have 4 exploitation, I’ve tried num3 but it’s not worked with me, so I’ve tried num2 and it’s worked well and get me reverse shell as you can see

by entering help you will get a list of available commands which you can use and by entering shell you will get a shell and then whoami to know our role

Good we’re root so we don’t need to more scripts to raise our privileges, let’s search for the root and the user flag in C:\Users

Congrats ❤
Stay in touch :)
Last updated